- VOX
- Technical Blogs
- Backup Exec
- Calling all CIOs | How prepared are you against Ra...
Calling all CIOs | How prepared are you against Ransomware?
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
With our constant internet usage and plethora of devices, there is more information being generated and shared than ever before. Also, because of the COVID-19 outbreak and majority of the workforce working at home, there are new security vulnerabilities that you need to be mindful of. As a result, the focus of cybercriminals has shifted and security solutions like Antivirus (AV) is no longer enough to be fully prepared against their sophisticated Ransomware attacks.
Now, don’t get me wrong. I’m not saying that security solutions are not required; in fact it is and will continue to be an important part of any Ransomware and cyberattack protection strategy, but the security landscape has changed a lot in the last couple of years, and you must implement more than ‘just’ AV to meet the challenges of today’s cyberthreats like Ransomware.
Today’s security landscape has changed, especially so in the past couple of years.
Customers require a more proactive attack protection to supplement basic AV. Using “just” AV or endpoint security product is like fighting with one arm tied behind your back. Note that Veritas Backup Exec has had its eye on the landscape and added protection technologies that are designed to help protect your critical data in case the worse happens.
In fact, When developing a framework for talking about Ransomware Resiliency, we’ve made the effort to align to language used by the NIST and CISA (Cybersecurity and Infrastructure Security Agency).
But do remember that NO single set of rules will protect every business, but thoughtful CIOs and CSOs take steps like these:
Educate:
Focus on employees training: Make sure your employees know the dangers and what to avoid. By 
Educate about how file-sharing programs and free downloads may install malicious code automatically. Stop them with training, policies, and software.
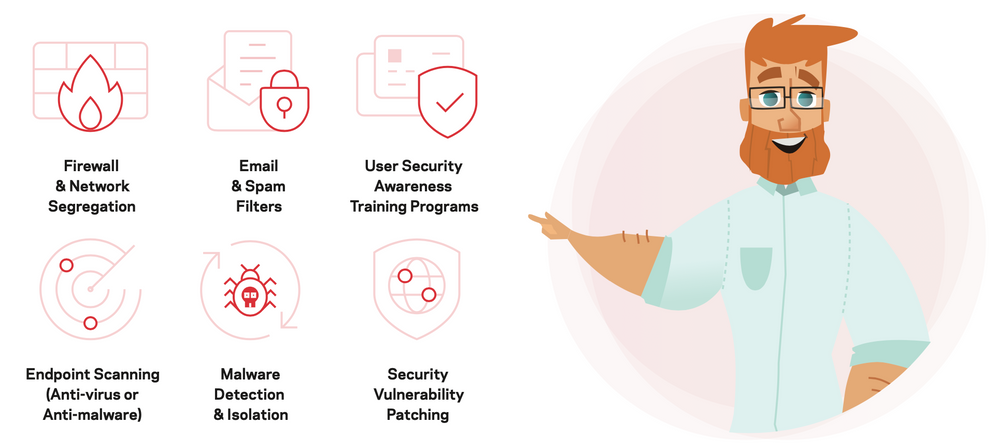
Secure:
Close security gaps: Protect network endpoints, not just perimeter. Make sure you analyse network traffic for signatures that match known cyberattacks.
- Integrate defenses: Combine Detection Systems (IDS), Intrusion Prevention Systems (IPS), AV, and firewall at endpoints – with encryption if they travel.
- Keep your OS/apps updated: Close vulnerabilities by quickly applying updates from software providers.
- Update virus definitions: Threats evolve – keep your AV software virus definitions up to date.
- Strong passwords: Make it mandatory to have strong passwords that mix letters and numbers and have policies in place to change them often.
Protect:
Regular backups: Implement and enforce backup schedules – and automate the process as much as possible.
- Follow 3-2-1 Rule and keep yours backups offsite: Be sure you can recover your files, systems, and survive loss of your facility, or even a regional disaster.
- Test your backups regularly: Don’t wait until actual data recovery to discover a technical shortcoming – test the entire backup and recovery cycle.
- Disaster Preparation Plan (DPP): Have a DPP return to an operational status as quickly as possible.
My final thoughts:
Though AV is not truly dead, it’s also not enough on its own. AV is a baseline capability required for any Rasnomware protection plan, but it’s just one piece that should be part of your broader arsenal to keep you and your information safe.
I am proud of the fact that we have a market-leading technology solutions like Backup Exec which has Ransomware Resiliency and that intelligence built into the solution to help protect your business better. Your businesses need more protection – not less – for your customers and employees, your reputation, and your business future.
If you want to learn more, I do encourage you to join me on my #WednesdayWebinar that is scheduled tomorrow (see details below) for How prepared are your against Ransomware attacks and why AV alone is NOT enough for changes in today’s Threat Landscape!
You will learn and see the ways systems are being infected today and mitigation steps you can take to protect your data and leverage #BackupExec within your environment which provides “assured recovery” from Ransomware!
Register for our LIVE #WednesdayWebinar:
How prepared are you against ransomware
Register ▻ https://bit.ly/BERansomware20
May 13 | 11:00 a.m. Singapore (GMT +8)
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
- Granular Ransomware Detection in NBU 10.4 in Protection
- Power-up ransomware resiliency with retention lock/WORM in Protection
- NetBackup support for detection of known Ransomware aware extension in Protection
- Securing Data and Infrastructure: A Comprehensive Approach in Protection
- Anomaly Detection in Backup Exec in Backup Exec