Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- VOX
- Technical Blogs
- Insights
- What Abraham Lincoln Teaches about Defensible Dele...
What Abraham Lincoln Teaches about Defensible Deletion of ESI
pfavro
Level 2
Options
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
11-19-2012
04:37 PM
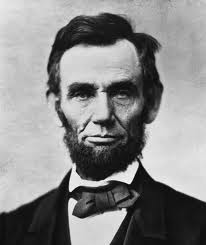 The reviews are in and movie critics are universally acclaiming Lincoln, the most recent Hollywood rendition regarding the sixteenth president of the United States. While viewers may or may not enjoy the movie, the focus on Abraham Lincoln brings to mind a rather key insight for organizations seeking to strengthen their defensible deletion process.
Lincoln has long been admired for his astute handling of the U.S. Civil War and for his inventive genius (he remains the only U.S. President who patented an invention). Nevertheless, it is Lincoln’s magnanimous, yet shrewd treatment of his rivals that provides the key lesson for organizations today. With a strategy that inexplicably escapes many organizations, Lincoln intelligently organized his documents and other materials so that he could timely retrieve them to help keep his political enemies in check.
This strategy was particularly successful with his Secretary of the Treasury, Salmon Chase, who constantly undermined Lincoln in an effort to bolster his own presidential aspirations. To blunt the effect of Chase’s treachery, Lincoln successfully wielded the weapon of information: Chase’s letters to Lincoln that were filled with problematic admissions. Doris Kearns Goodwin chronicled in her Pulitzer Prize winning book, Team of Rivals, how Lincoln always seemed to access that information at a moment’s notice to save him from Chase’s duplicity.
Lincoln’s tactics reinforce the value of retaining and retrieving important information in a time of need. Lacking the organizational and technological capacity to do so may prevent companies from pulling up information at a crucial moment, be it for business, legal or regulatory purposes. For this and many other reasons, industry experts are recommending that organizations implement a defensible deletion strategy.
Defensible Deletion Requires Deletion
Such a strategy could have some success if it is powered by the latest in effective retention technologies such as data classification and automated legal hold. Such innovations will better enable organizations to segregate and preserve business critical ESI.
And yet, it is not enough to just adopt the preservation side of this strategy, for the heart of defensible deletion requires just that – deleting large classes of superfluous, duplicative and harmful data – if its benefits are ever to be realized. Companies that fail to delete such ESI will likely never come off conqueror in the “battle of the data bulge.” Indeed, such a growing waistline of data is problematic for three reasons. First, it can place undue pressure on an organization’s storage infrastructure and needlessly increase the cost of data retention. It can also result in higher eDiscovery costs as the organization is forced to review and analyze all of that ESI largesse. Finally, a potentially fatal risk of producing harmful materials – kept beyond the time required by law – in eDiscovery will unnecessarily increase. All of which could have been obviated had the enterprise observed the rule of “good corporate housekeeping” by eliminating ESI in a manner approved by courts and the rules makers.
For organizations willing to get rid of their digital clutter, defensible deletion offers just what they need so as to reduce the costs and risks of bloated ESI retention. Doing so will help companies make better use that information so, like Honest Abe, they can stave off troublesome challenges threatening the enterprise.
The reviews are in and movie critics are universally acclaiming Lincoln, the most recent Hollywood rendition regarding the sixteenth president of the United States. While viewers may or may not enjoy the movie, the focus on Abraham Lincoln brings to mind a rather key insight for organizations seeking to strengthen their defensible deletion process.
Lincoln has long been admired for his astute handling of the U.S. Civil War and for his inventive genius (he remains the only U.S. President who patented an invention). Nevertheless, it is Lincoln’s magnanimous, yet shrewd treatment of his rivals that provides the key lesson for organizations today. With a strategy that inexplicably escapes many organizations, Lincoln intelligently organized his documents and other materials so that he could timely retrieve them to help keep his political enemies in check.
This strategy was particularly successful with his Secretary of the Treasury, Salmon Chase, who constantly undermined Lincoln in an effort to bolster his own presidential aspirations. To blunt the effect of Chase’s treachery, Lincoln successfully wielded the weapon of information: Chase’s letters to Lincoln that were filled with problematic admissions. Doris Kearns Goodwin chronicled in her Pulitzer Prize winning book, Team of Rivals, how Lincoln always seemed to access that information at a moment’s notice to save him from Chase’s duplicity.
Lincoln’s tactics reinforce the value of retaining and retrieving important information in a time of need. Lacking the organizational and technological capacity to do so may prevent companies from pulling up information at a crucial moment, be it for business, legal or regulatory purposes. For this and many other reasons, industry experts are recommending that organizations implement a defensible deletion strategy.
Defensible Deletion Requires Deletion
Such a strategy could have some success if it is powered by the latest in effective retention technologies such as data classification and automated legal hold. Such innovations will better enable organizations to segregate and preserve business critical ESI.
And yet, it is not enough to just adopt the preservation side of this strategy, for the heart of defensible deletion requires just that – deleting large classes of superfluous, duplicative and harmful data – if its benefits are ever to be realized. Companies that fail to delete such ESI will likely never come off conqueror in the “battle of the data bulge.” Indeed, such a growing waistline of data is problematic for three reasons. First, it can place undue pressure on an organization’s storage infrastructure and needlessly increase the cost of data retention. It can also result in higher eDiscovery costs as the organization is forced to review and analyze all of that ESI largesse. Finally, a potentially fatal risk of producing harmful materials – kept beyond the time required by law – in eDiscovery will unnecessarily increase. All of which could have been obviated had the enterprise observed the rule of “good corporate housekeeping” by eliminating ESI in a manner approved by courts and the rules makers.
For organizations willing to get rid of their digital clutter, defensible deletion offers just what they need so as to reduce the costs and risks of bloated ESI retention. Doing so will help companies make better use that information so, like Honest Abe, they can stave off troublesome challenges threatening the enterprise.
Labels:
-
archive
-
Archiving
-
Archiving Software
-
automated legal hold
-
Best Practices
-
Clearwell
-
Data Classification
-
Data Retention
-
data set
-
defensibility
-
defensible deletion
-
defensible e-discovery
-
discoverable
-
discovery
-
Document Retention
-
document review
-
e-discovery
-
e-discovery software
-
e-mail
-
eDisclosure
-
eDiscovery
-
ediscovery software
-
electronic data discovery
-
electronic discovery
-
Electronic Discovery Best Practices
-
electronically stored information
-
Email
-
email archive
-
Enterprise Vault
-
esi
-
Information Governance
-
Information Retention
-
legal discovery
-
Litigation
-
litigation discovery
-
Preservation
-
retention policy
-
symantec
-
Symantec eDiscovery Blog
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
Related Content
- Unparalleled insights driving downstream discovery, compliance, and storage optimization in Insights
- Best practices for enterprise data management: creating a data governance strategy in Insights
- Enterprise Vault 12 – It’s Not Just for Storage Anymore in Insights
- There’s Gold in Them Thar Hills in Insights
- Classification: All data is not created equal in Insights

