- VOX
- Technical Blogs
- Insights
- Interoperability of Veritas Data Insight and Syman...
Interoperability of Veritas Data Insight and Symantec's Data Loss Prevention configuration tips
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Note: All hyperlinks in this document need to be run on the Management server directly or modified to change localhost to the hostname of that server unless noted as public. They are provided for ease of use after export or to be copied exactly to a customer's DI environment. To modify to run on a newer environment for example 6.0x then change 5_2 and DI5.2 to 6_0 and DI6.0 within the URL. The Admin can also search the title in the online help after it is accessed.
Note: All footnotes(#) are references within the document to information from the link reference. If you prefer you may scroll to the bottom of the article and read the reference designated as (#) inline.
Note: The document attached can be imported into the Data Insight environment locally and utilized as is on the Management Server (MS). This document is created from proprietary knowledge, the available version specific online help and consultation with notes or testing.
Data Insight 5.2 Administration is specifically discussed but the steps are applicable to DI4.5x and DLP12.5x and newer versions.
Test case was DI5.2 and DLP 14.6.
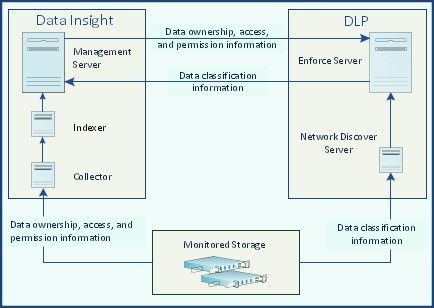
Symantec Data Loss Prevention (DLP) helps you detect potential breach of sensitive data from your environment. The DLP Network Discover Server scans files on your NAS devices and generates incidents with details of the files that violate DLP policies. Data Insight tracks the users that could have access to file objects on those same NAS devices, those users who have used that access and from where it was accessed, who the file owner is and other values that can be configured into the lookup map by the DLP application.
Figure: Data Insight- DLP integration
DI has a bi-directional integration with DLP. Based on requirements you can integrate the two products in either or both of the following ways:
- Configure DLP in Data Insight:
DLP provides DI the information about sensitive files in a storage environment monitored by both DI and DLP. Data Insight runs the DLPSensitiveFilesJob at 12:00 A.M. every night to retrieve a list of sensitive files from the DLP environment. DI uses this information to raise alerts in response to configured DLP policies.
The information about sensitive files and DLP policies is used to calculate the risk-scores for storage resources and their users. The risk-scores and related information are displayed on the dashboard view of the Data Insight Management Console. You can use this information to find the high-risk shares and the folders that violate important DLP policies. Additionally, you can use the information from DLP to define DLP Incident Remediation workflow to take action on the files that violate certain DLP policies.
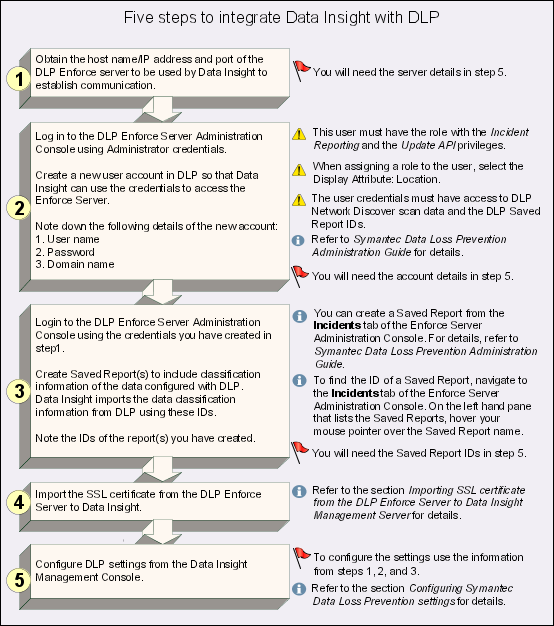
To configure Data Insight to fetch sensitive files information from DLP, complete the following tasks:
- Configure DLP settings from the Data Insight Management Console.
See Configuring Symantec Data Loss Prevention settings (1)
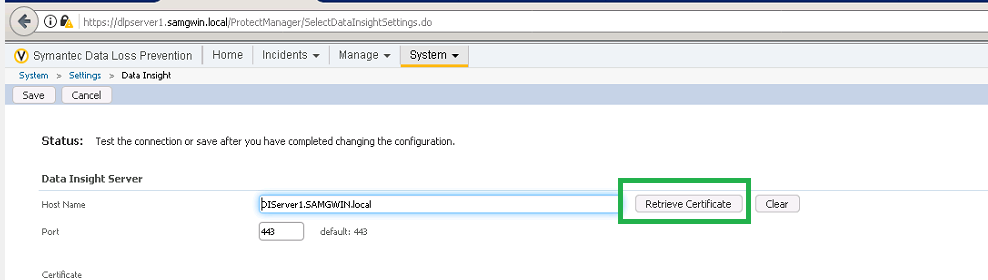
- Import the SSL certificate from the DLP Enforce Server to Data Insight.
See Importing SSL certificate from the DLP Enforce Server to Data Insight Management Server (2)
Figure: Data Insight - DLP integration workflow for data transfer
See About configuring Data Insight to integrate with Data Loss Prevention (DLP)
- Configure Data Insight in DLP:
Data Insight provides DLP ownership, access and permission-related information which is used to generate folder risk reports and to display ownership information against incidents.
See About Symantec Data Loss Prevention (DLP) integration with Data Insight
Complete the following tasks in DLP to configure DLP to pull access data from Data Insight:
- Configure a connection between the DLP Enforce Server and Data Insight.
- Configure the Data Insight Lookup Plug-in to retrieve data owner information.
- Configure other lookup plug-ins to populate the Data Owner email field in Data Insight.
Refer to the Symantec™ Data Loss Prevention Administration Guide (Public manuals) for details on configuring these plug-ins.
- On the Enforce Server, create custom attributes for each file detail that you want retrieved from the Data Insight Management Server.
- Map the custom attributes that you have created to the details from the Data Insight Management Server.
- Restart the DLP Enforce services.
The steps mentioned in this section are applicable for DLP users who want to pull data ownership, permissions and access information from Data Insight. For the detailed steps, see the Data Loss Prevention Data Insight Implementation Guide i.e. version14.6. (Public manuals)
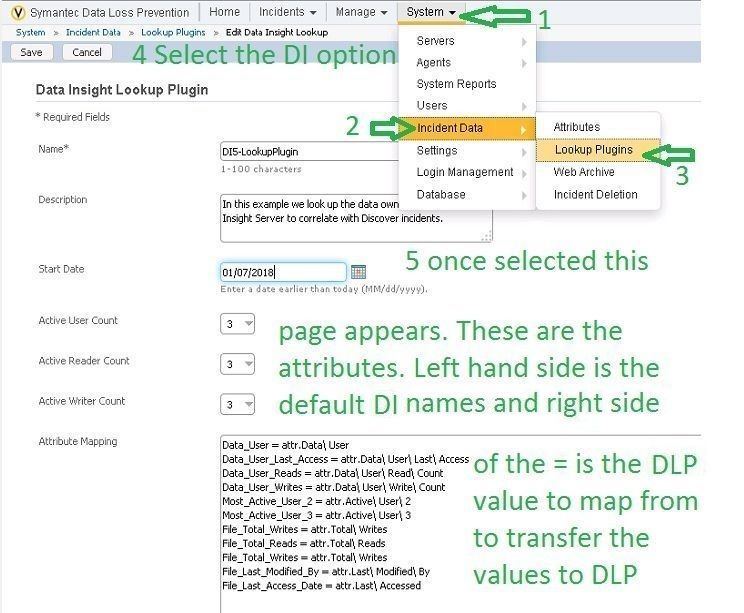
To complete the configuration the Administrator has to configure the lookup properties stored in the DLP database to map to the actual values in the DI databases for the file objects referenced in the incidents.
An example of the plugin mappings to use is below:
Data_User = attr.Data\ User
Data_User_Last_Access = attr.Data\ User\ Last\ Access
Data_User_Reads = attr.Data\ User\ Read\ Count
Data_User_Writes = attr.Data\ User\ Write\ Count
Most_Active_User_2 = attr.Active\ User\ 2
Most_Active_User_3 = attr.Active\ User\ 3
File_Total_Writes = attr.Total\ Writes
File_Total_Reads = attr.Total\ Reads
File_Total_Writes = attr.Total\ Writes
File_Last_Modified_By = attr.Last\ Modified\ By
File_Last_Access_Date = attr.Last\ Accessed
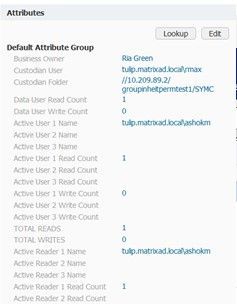
you can paste them into the window. Once there is a proper connection and the lookup is functional all the incidents with mating DI attributes should populate and appear similar to this diagram:
To troubleshoot it has been done correctly review the below steps:
Troubleshoot Role Configuration
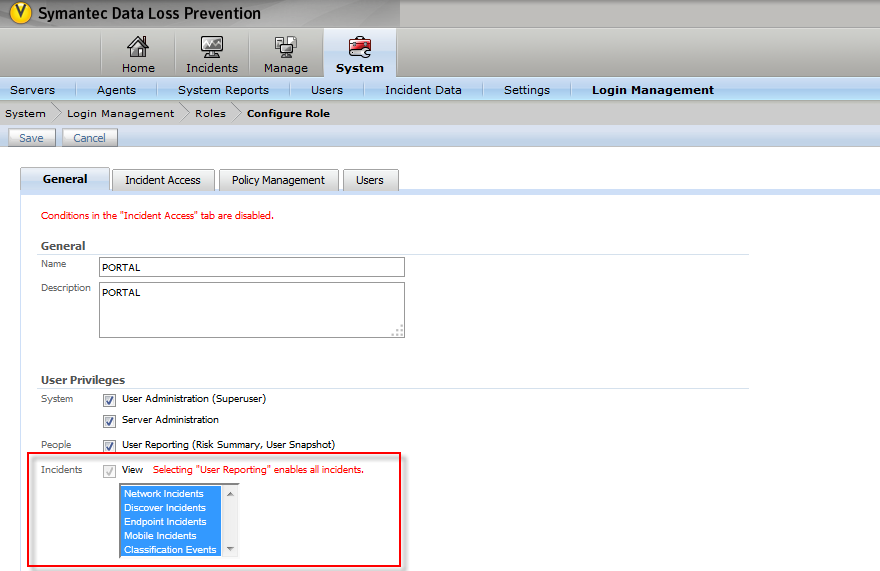
Role configuration in DLP:
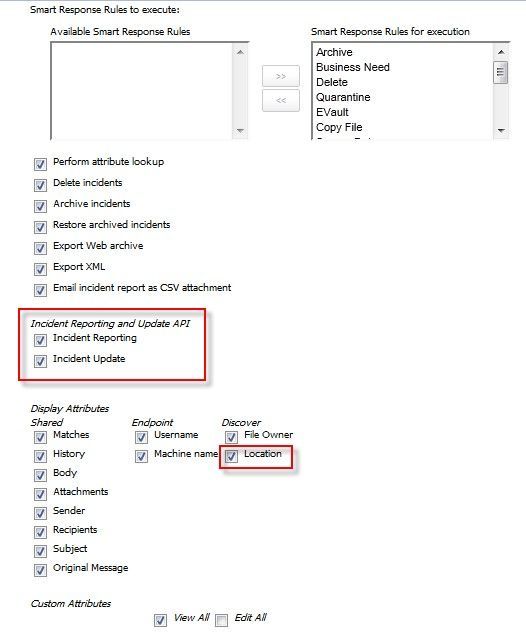
Ensure that user privilege ‘Incident’ is enabled as a part of role configuration.
Ensure that user must have the role with Incident Reporting & Update API privileges. Also the display attribute Location has to be selected.
How to Find Out Saved Report ID
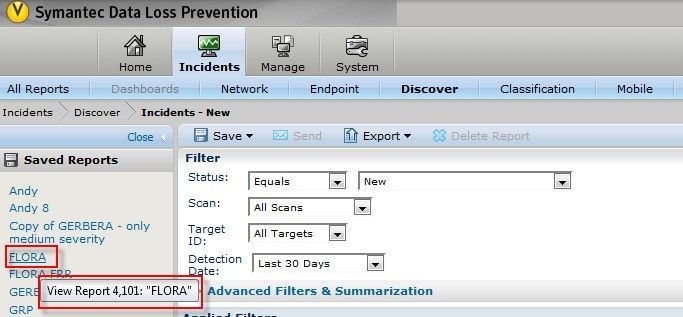
To find the ID of a Saved Report, navigate to the Incidents tab of the Enforce Server Administration Console. On the left hand pane that lists the Saved Reports, hover your mouse pointer over the Saved Report name
Note: Log files for DataInsight
Review below log files present at “C:\Program Files\Symantec\DataInsight\log” by default on the Management Server node which hosts the console.
cli0.0.log : To troubleshoot DlpSensitiveFilesJob (job which pulls DLP Sensitive file details from DLP) related issues.
webserver0.0.log & commd0.0.log: To troubleshoot DLP connection failure issue.
Last steps would be the use the Self-Service Portal (3) (requires a separate license) to manage DLP incidents and delegate workflow. To view the complete workflow for setting up Data Insight to integrate with DLP for remdiation, refer to Managing workflows under the link explanation which is planned for a future Blog article.
Footnotes.
Designed for users who do not have access to the internal online help within their environment.
(1) You must configure the settings that allow Data Insight to communicate with Symantec Data Loss Prevention.
To configure Data Loss Prevention settings
- In the Management Console, click Settings > Data Loss Prevention.
- Click Edit, and enter the following details:
- Hostname /IP address of DLP Server
The host name or IP address of the DLP Enforce Server. DLP host names are case-sensitive.
- Port
The port through which Data Insight connects to the DLP Enforce Server.
The default port number is 443.
- Username
The user name of the account that is used to access the DLP Enforce Server. DLP user names are case-sensitive.
Ensure that the credentials belong to an existing DLP user assigned the Incident Reporting and Update API role. Also ensure that when assigning a role to the user, the Display Attribute Location is selected. This attribute allows Data Insight to view the complete path of a file.
The user credential being used must have access to DLP Network Discover scan data and DLP Saved Report IDs.
- Password
The password of the account that is used to access the DLP Enforce Server.
- Domain
The name of the domain to which the user belongs. DLP domains are case-sensitive.
Specifying the domain is optional for a user who is a DLP administrator.
- DLP Role
Specify the role you want to use to log on to DLP. DLP roles are case-sensitive.
Users who are assigned more than one role can only log on under one role at a time.
- Configure storage resources automatically
By default, Data Insight discards classification information for paths on storage devices that it does not monitor. Select this option to add the unmonitored devices as generic devices in Data Insight and include classification information for all paths on those devices. Note that only data classification information is available for the paths. To enable Data Insight to get audit and metadata information for the paths, you must manually configure the devices in Data Insight to match those in DLP.
- Saved Report IDs
Enter a comma-separated list of Saved Report IDs in DLP.
Data Insight fetches classification information for all the paths present in the DLP Saved Report. Data Insight uses the DLP Reporting API Web service to request a list of incident IDs by specifying a saved report ID. A Data Insight process then fetches the sensitive files corresponding to the incident IDs.
- Click Test Connection to verify the connection to the DLP Enforce Server.
- Click Save to save the settings.
(2) Importing SSL certificate from the DLP Enforce Server to Data Insight Management Server
The DLP Enforce Server administration console requires SSL transport for all communication. Data Insight must be able to negotiate the SSL connection with the Enforce Server. For this purpose, you must import the certificate to the keystore used by Data Insight.
To import the SSL certificate from the DLP Enforce Server to Data Insight using Firefox
- Type the URL to connect to a DLP Enforce Server Administration console.
- On the security certificate warning page, click I understand the risks.
- Click Add Exception.
- On the Add Security Exception page, click View to view the certificate details.
- Click the Details tab and click Export.
- From the Save as type drop-down, select X.509 Certificate (DER).
- Click Save.
To import the SSL certificate using Internet Explorer
- Type the URL to connect to a DLP Enforce Server Administration console.
- On the security certificate warning page, click Certificate Error next to address bar.
- Select View certificates.
- Click the Details tab, and select the appropriate certificate.
- Click Copy to File
- In the Certificate Export Wizard, select DER encoded binary.
- Click Next.
- Enter the name of the file and browse to the location where you want to save the file.
- Click Next
- Click Finish to save the file.
After the SSL certificate is imported, complete the following steps to import the SSL certificate on the Data Insight server.
To import the SSL certificate on the Data Insight server
- From the Windows Start menu, select Run and type cmd in the dialog box to open a command prompt window.
- Run the following command:
cd C:\Program Files\DataInsight\jre\bin
.\keytool -importcert -alias dlp -keystore c:\ DataInsight\data\keys\commd.keystore -trustcacerts -file <file path of SSL certificate>
Specify changeit as the password for the keystore.
You can now pull a list of sensitive files from Symantec Data Loss Prevention (DLP).
(3) Using the Self-Service Portal to manage Data Loss Prevention (DLP) incidents
You can use the Self-Service Portal to remediate incidents on the paths that are assigned to you. On the DLP Incident Remediation page of the portal, you can do following tasks:
- View a snapshot of the number of files that are assigned for your attention. The files are sorted according to the severity of incidents that are associated with them.
- Filter the list of files based on the severity of the incidents that the files have violated, the recency of the last access date, or the DLP policy that the files violate. The filters available to you depend on the options that are selected when configuring the workflow template.
The different filters are applied together, and the list is filtered to show the data that matches the applied criteria.
- Perform a configured action on multiple files at one time. The available actions are DLP Smart Response rules configured in DLP. You can select more than one file from the list and then choose the desired action.
To remediate the files
- Select the files that you want to remediate.
You can choose to filter the list of files using the filter criteria at the top of the page. For example, you can prioritize the remediation of files that are associated with high severity incidents that violate a particular policy. Files that match the selected filter criteria are listed. Select the desired files from the list.
- From the Select Action drop-down, select the action that you want to take on the selected files. For example, you may quarantine the files or mark the files for deletion. The listed actions are the Smart Response rules that are configured within DLP.
For more information about Smart Response rules, see the Symantec Data Loss Prevention Administration Guide.
- Click Submit to send the remediation request to the Data Insight Management Server for further action.
On submission of the request, the actions that you select are sent to the Data Insight Management Server, which in turn requests the Response Rule Execution Service running on the DLP Enforce Server to execute the response rules. You can view the status of the workflow on the Data Insight Management Console.
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
- Deliver Operational Efficiency and End-To-End Resilience with NetBackup Flex 2.1 in Protection
- 3 Powerful Steps to Boost Your Backup With Cloud in Protection
- Windows Server 2003 Migration Challenges and Options - Part 2 in Partners
- Windows Server 2003 Migration Challenges and Options - Part 2 in Enterprise Data Services Community Blog