Granular Ransomware Detection in NBU 10.4
Rapid detection of ransomware attacks is an essential component of a comprehensive cyber resilient solution. These attacks have the following basic life-cycle: (i) utilize some vulnerability to infilt...
Rapid detection of ransomware attacks is an essential component of a comprehensive cyber resilient solution. These attacks have the following basic life-cycle: (i) utilize some vulnerability to infilt...
“Data is the new oil”, which is why data protection becomes crucial for organizations, government, and businesses. Backup Exec, a leader in the small to mid-size business segment is aligned to its com...

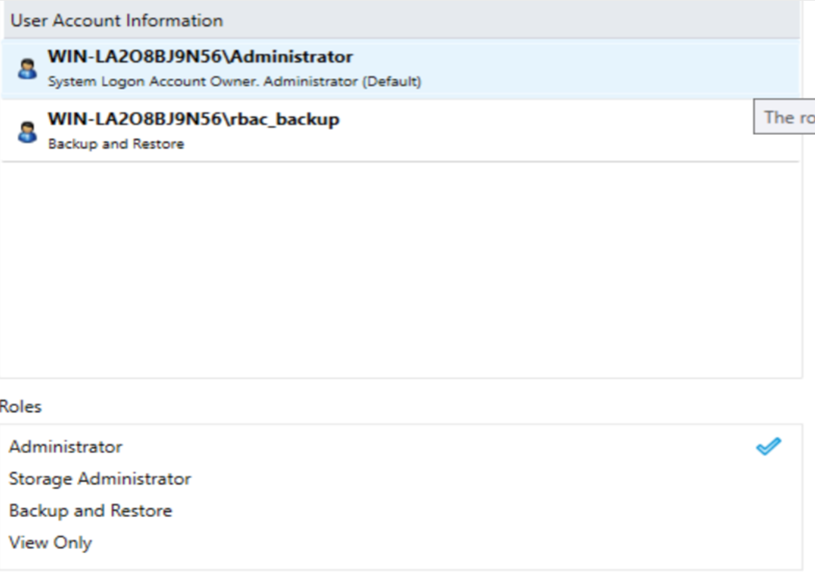
With the latest release of Backup Exec, Role-based Access Control (RBAC) is introduced in the product. Organizations have different users who manage their backup environment. Each user is designated t...
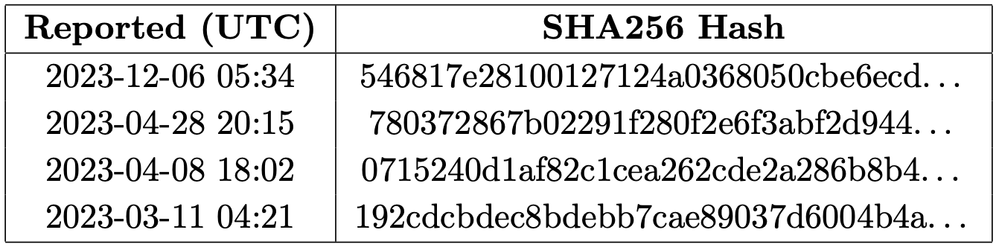
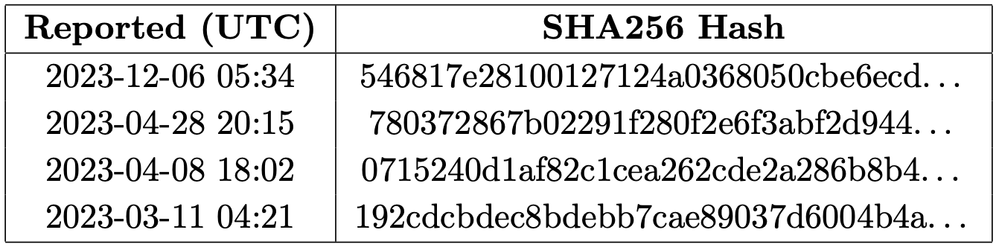
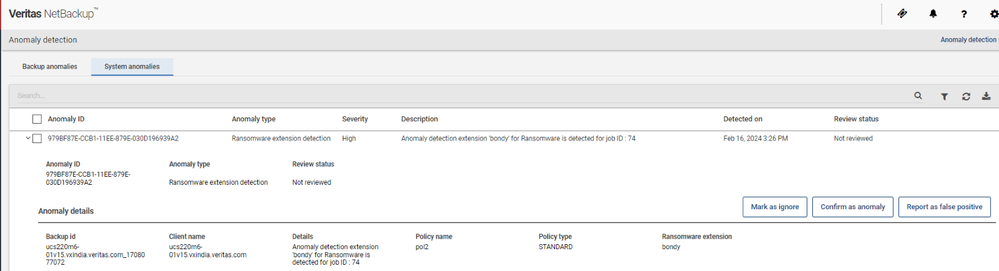
Typically, when a ransomware attacks a system, it encrypts the data which could be in the form of document files such as pdf, doc, excel or text files. Those attacks add extension to the encrypted fil...
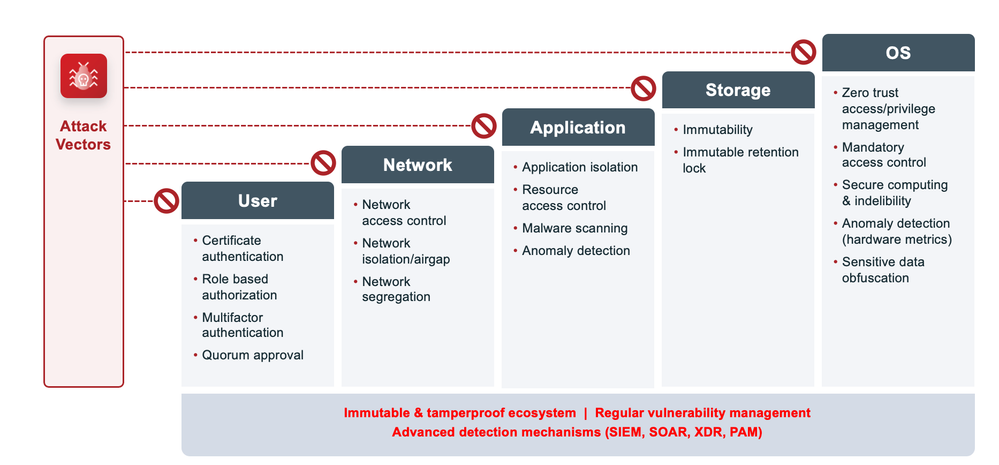
Security of data and infrastructure has become a world in itself. Everyone talks about so many terms that it’s easy to feel overwhelmed by the possibilities of securing your data. At the same time, yo...
Backup Exec 22.2 brings you faster virtual machine backups powered by ReFS block cloning technology. Consolidate full backups with the help of ReFS block cloning deliver up to 95% of performance impro...

Are you worried about the cost of a site failure and the stress it puts on you to quickly get your environment back up and running? Recovering from site failures often requires numerous manual and ted...

Take Action On Day 1 To Recover Oh, we got hacked. The following process is a general guide describing what to do during this devastating time. Isolate the Infection Most of the ransomwares will scan ...

Five Key Steps in Defining a Cyber-recovery Strategy Cyber Incident Response Teams must be well-equipped with the right tools and knowledge to manage a ransomware attack and ensure the recovery of the...

Quickly map your security assessment and find gaps that remain uncovered is a key to improve your security posture. And Veritas Appliance security meter can do this for you and also I included ten tip...
