- VOX
- Technical Blogs
- Insights
- Reduce risk with the data visibility, search, and ...
Reduce risk with the data visibility, search, and delete capabilities of Information Studio 1.1
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Today, many enterprises maintain complex data landscapes that include multi-cloud architecture and a diverse storage infrastructure. Due to massive data growth and increasing data privacy, country and vertical-specific regulations, organizations are seeking ways to visualize the data in their infrastructure and reduce risk.
Information Studio offers clear visibility, targeted analysis, and informed action on data from a variety of cloud and on-premise data sources. This allows organizations to confidently address personal data security concerns, oncoming regulations, and continued data growth.
Information Studio 1.1 focuses on securely providing organizations enhanced visibility, search and delete capabilities needed to respond to data privacy or regulatory requests, reducing risk.
Enhanced visibility
Information Studio 1.1 adds the ability to visualize and filter on NetBackup Policies.
In addition to exporting reports from the UI, authorized users can leverage an API for text or regex queries to filter through the data and create a downloadable report.
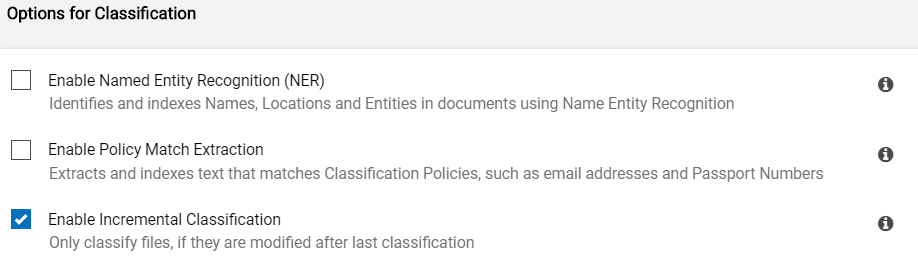
Information Studio 1.1 greatly increases the amount of visibility it provides, helping you to respond quicker to data privacy requests and other legislation. It does this with new classification options, including Policy Match Extraction, Named Entity Recognition (NER) and Incremental Classification.
Let's dig into each of these options:
Classification Option: Named Entity Recognition
If the classification option “Named Entity Recognition (NER)” is enabled, as the classification job is reading the text it will use context to also identify names, organizations and locations. It stores these entities as additional metadata tags categorized as name-tag, organization-tag and location-tag. NER isn't reliant on finding policy matches and as such can find names, organizations and locations even when a file doesn't have any classification tags.
Classification Option: Policy Match Extraction
When conditions are met within a policy the tag associated with the policy is stored. With the classification option “Policy Match Extraction” enabled, it also stores the text strings matching the conditions and stores it as metadata tags. As an example, lets say a policy is enabled to identify mailing and email addresses; if found, it adds a PII metadata tag.
- With “Policy Match Extraction” disabled only the “PII” tag would be added
- With “Policy Match Extraction” enabled it would add the “PII” tag and “555 Kensington Avenue, London, Ontario, M3C 4K5, Canada” and jdoe@acme.corp tags, which were found as pattern matches to the enabled policy.
Classification Option: Incremental Classification
The Incremental Classification option adds the ability to add new policies or options at a later date and rerun classification on data already classified. This is useful for situations when you want to reclassify data because:
- New policies are added
- New options (Enable NER or Policy Match Extraction) are enabled
- Business needs change and require a new custom policy be added to find a specific pattern
For more information on the more than 120 policies and 700 preconfigured patterns that identify common data privacy and regulatory compliance principles refer to my previous blog.
Enhanced search capabiltiies
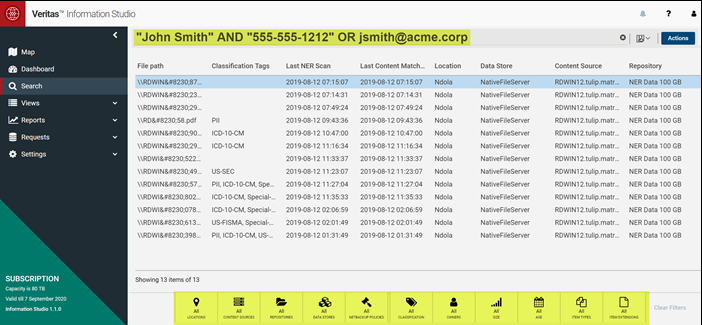
Information Studio 1.1 enhances its search capabilities allowing both filtering using item attributes as well as text and regex searches.
Filtering within the Information Studio dashboard helps identify many types of information including non-business, orphaned, stale data, data protected by a specific NetBackup policy, items older than a specific range, data containing PII or regulatory information, etc... However, there are times that it is important to be able find other specific information. As an example, to respond to subject access requests (SAR) or investigations it is important to be able to search for data that contains specific text strings like a person's name or other specific personal information.
Information Studio 1.1 adds the ability for authorized users to search for text strings stored as a result of Policy Match Extraction and Named Entity Recognition. Search queries support both text and regex with conjunctions (AND & OR) using any kind and level of hierarchy. Further filtering is available and is shown highlighted at the bottom of this screen shot.
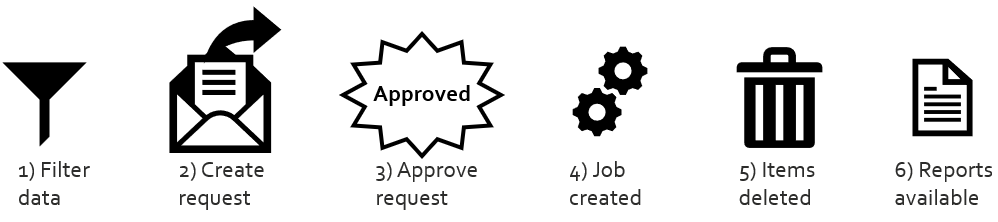
Reduce risk
Beyond finding risky information, Information Studio 1.1 delivers evidence-driven decisions to defensibly delete data and reduce risk. Don't worry, you can limit who has the authority to delete files, and Information Studio keeps an audit trail of this activity. As an example, an authorized user may filter for items containing special categories of personal data for EU residents stored in Asia. Unless the organization has a lawful basis to process these special categories of personal data for EU residents, this would violate GDPR and therefore require it to be deleted.
- First authorized users filter through the data to identify files that should be deleted.
- Then the user selects to create a delete request. This action is only visible to users with the specific permission to create a delete request.
- Then another user, with the specific permission to review the request receives an email notification about the request. Using their credentials, they can decide whether to approve the request or not. If they approve it, approval confirmation is required.
- If the request is approved Information Studio will spawn creation of a job
- Information Studio will schedule to delete these files.
- Details about the request and an audit log will be saved. This includes information about who made and who approved the request. It also provides the ability to download status details about each file contained within the delete action including content source, repository, filename, status and (if applicable) failure reason.
Note: Currently deletion is only supported for files in CIFS shares. Files stored on other data sources can be identified and a list exported using Information Studio for manual review and deletion.
Increased security
Information Studio 1.1 added support for custom role creation, authorized users can create a role and explicitly add permissions. Roles are assigned to users, locally or via Active Directory. Examples of these roles include the ability to use API calls, to perform searches, to create or approve data delete operations, etc…
Information Studio 1.1 also added support for user certificate-based two-factor authentication (2FA) over the HTTPS interface.
For more information check out my white paper.
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
- Understand, Plan and Rehearse Ransomware Resilience series - Design to Recover in Protection
- Understand, Plan and Rehearse Ransomware Resilience series - Access and Improve in Protection
- Backup Exec 22.1 Protects Microsoft Teams in Backup Exec
- Find out what’s new in Veritas NetInsights Console (System Health Insights) in Protection
- Veritas Backup Exec 22 Delivers Day-one Support for vSphere 8.0 in Backup Exec